 This new book focusses on how to technically secure PII (Personal Identifiable Information) in your computer business systems. It’s full of practical advice and techniques on how to discover PII, categorise it, collate it and finally secure it.
This new book focusses on how to technically secure PII (Personal Identifiable Information) in your computer business systems. It’s full of practical advice and techniques on how to discover PII, categorise it, collate it and finally secure it.
The book is based on many years of practical experience dealing with personal data and keeping it secure. It combines both security and architectural techniques in securing information.
With such a book you can have a high degree of confidence your IT security approach is correct in how it handles PII and is future proofed.
It also covers security techniques from first principals. This book is equally suited to management, IT professionals and students alike. Plenty of references are provided and all terms are defined in plain English.
Chapters:
- Chapter 1 – What’s PII and Why all the Fuss?
- Chapter 2 – Information Analysis
- Chapter 3 – Regulations & PII
- Chapter 4 – Business Investment Case
- Chapter 5 – PII Discovery
- Chapter 6 – PII Analysis
- Chapter 7 – Core Information Security Principals
- Chapter 8 – PII Anti-Patterns
- Chapter 9 – PII Strategies
- Chapter 10 – PII Anonymisation
- Chapter 11 – Putting it all Together
- Chapter 12 – The PII Vault
- Chapter 13 – Future Trends
271 pages in length, published in both eBook ($23.99 USD) and Paperback ($37.99 USD).
EBook: Amazon US
Paperback: Amazon US (includes the eBook for free)
Related Products
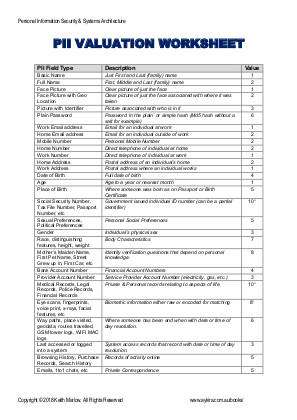
A PDF of the PII Field to Value table on pages 79 to 80 of the 'Personal Information Security & Systems Architecture' book, with on the back details of how you utilise the table to value your PII data.
The idea is you print this out and laminate it, so it makes it an easy to use point of access independent of the book - also saving wear and tear on the book if you have the physical copy. If you are using the eBook, it will save you being dependent on an eBook reader to use the table. It's just easier all round to use a printed full-size copy.
Purchasing this PDF gives you a licence for you to use directly as part of your work, it does not give you the rights to reproduce and copy for others to use.